Webhooks let you receive real-time events when a new deployment is created. Use them to trigger CI/CD steps, purge caches, notify downstream systems, or kick off analytics pipelines — all automatically when a prompt is deployed or rolled back.Documentation Index
Fetch the complete documentation index at: https://www.adaline.ai/docs/llms.txt
Use this file to discover all available pages before exploring further.
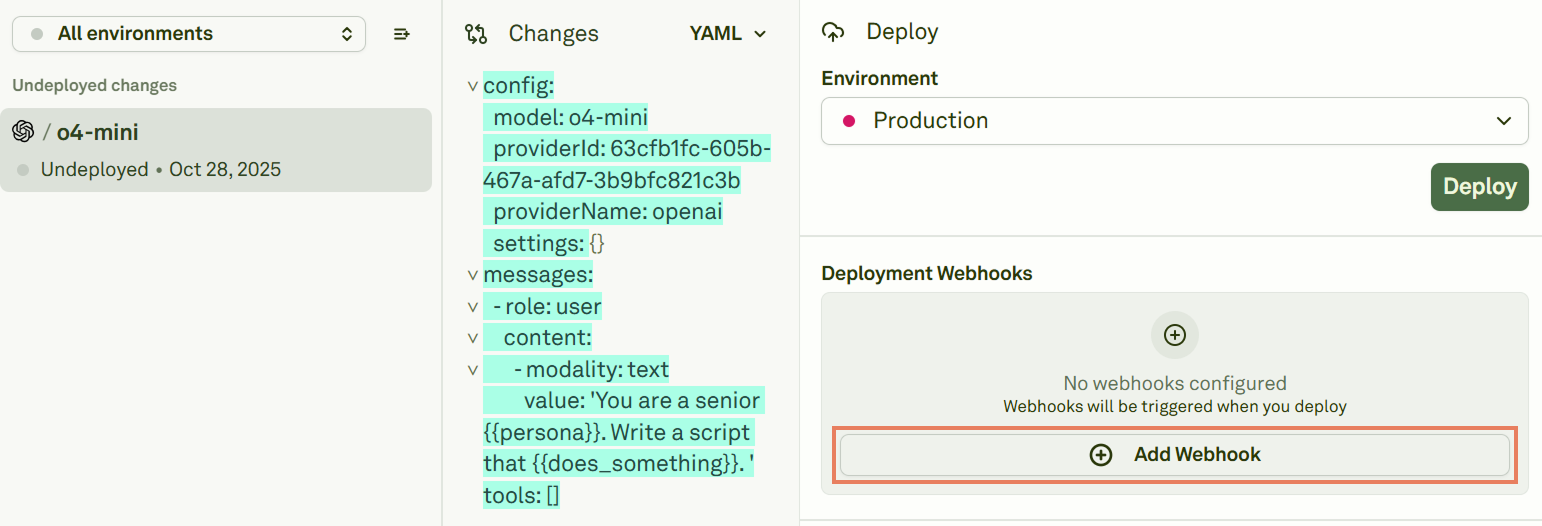
Create a webhook
You can create webhooks from two places: From project settings — Click Settings on Adaline’s main page and find the Webhooks section under your project: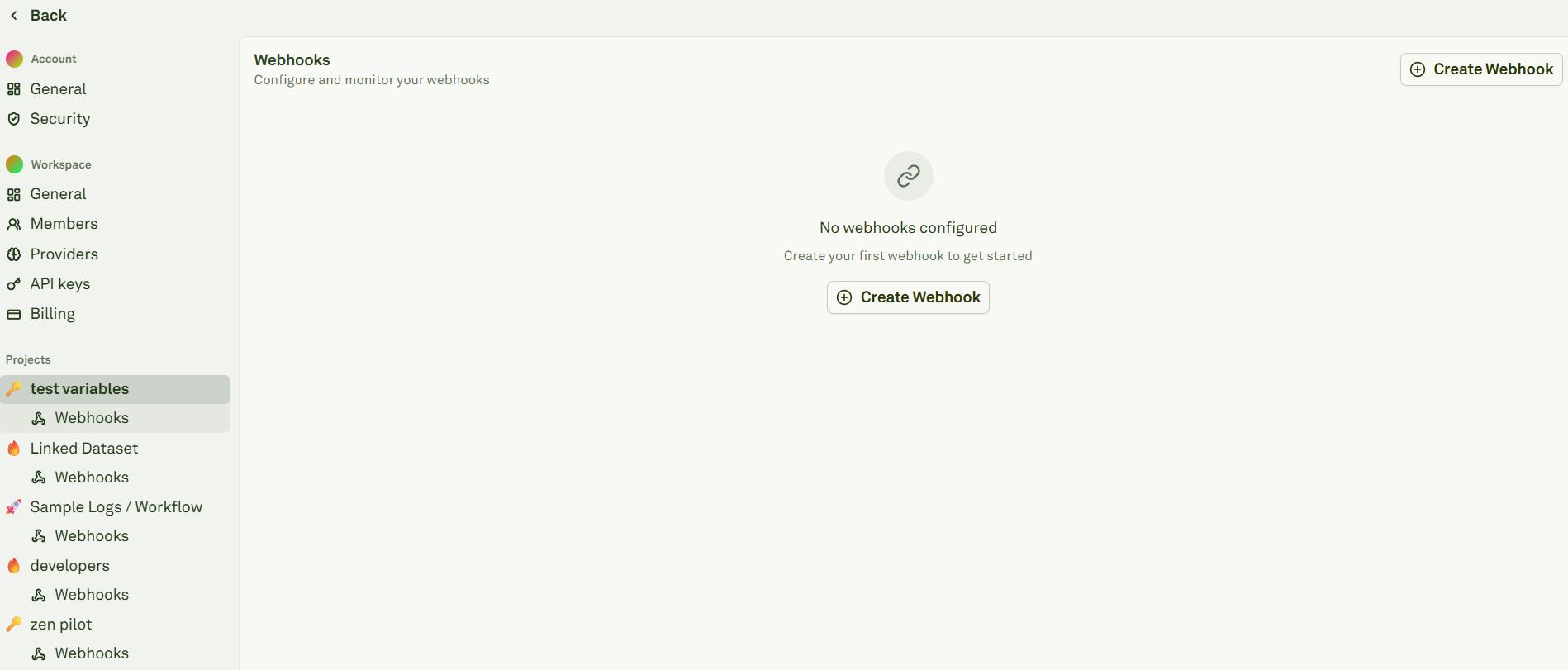
Configure a webhook
When creating a new webhook, fill in the following fields: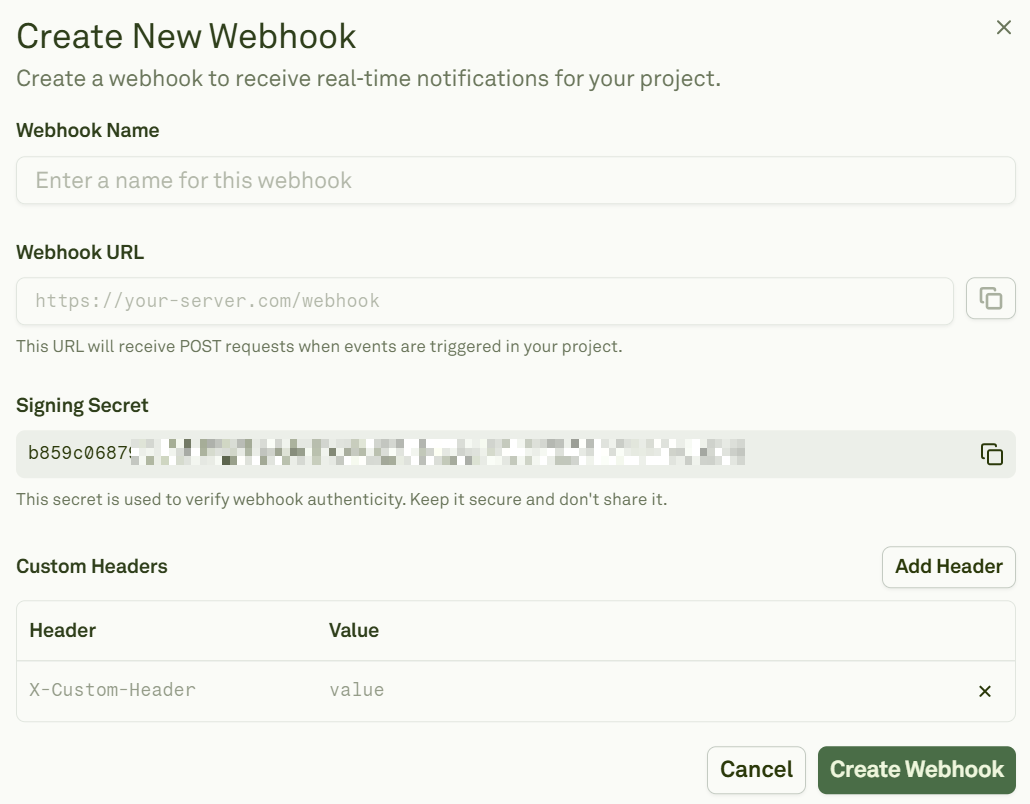
| Field | Description |
|---|---|
| Webhook Name | A short, descriptive name for the destination. |
| Webhook URL | The HTTPS endpoint that will receive events. |
| Signing Secret | Auto-generated by Adaline. Copy and store it securely — you’ll use it to verify signatures. |
| Custom Headers | Add any custom headers your endpoint expects (e.g., authorization tokens). |
create-deployment event.
Event format
Currently, Adaline emits a single project event:create-deployment. This event fires whenever a new deployment snapshot is created for a prompt and environment.
Request details
| Setting | Value |
|---|---|
| Method | POST (JSON body) |
| Content-Type | application/json |
| Signature header | X-Webhook-Signature |
Verify signatures
When a payload is present, Adaline attaches anX-Webhook-Signature header. The value contains a timestamp and one or more signatures (to support secret rotation):
rawBody— The exact request body string.signatureHeader— TheX-Webhook-Signatureheader value.secret— Your signing secret from the webhook configuration.
Test webhooks
From the webhook details page, click Send Test Event to confirm connectivity and signature validation: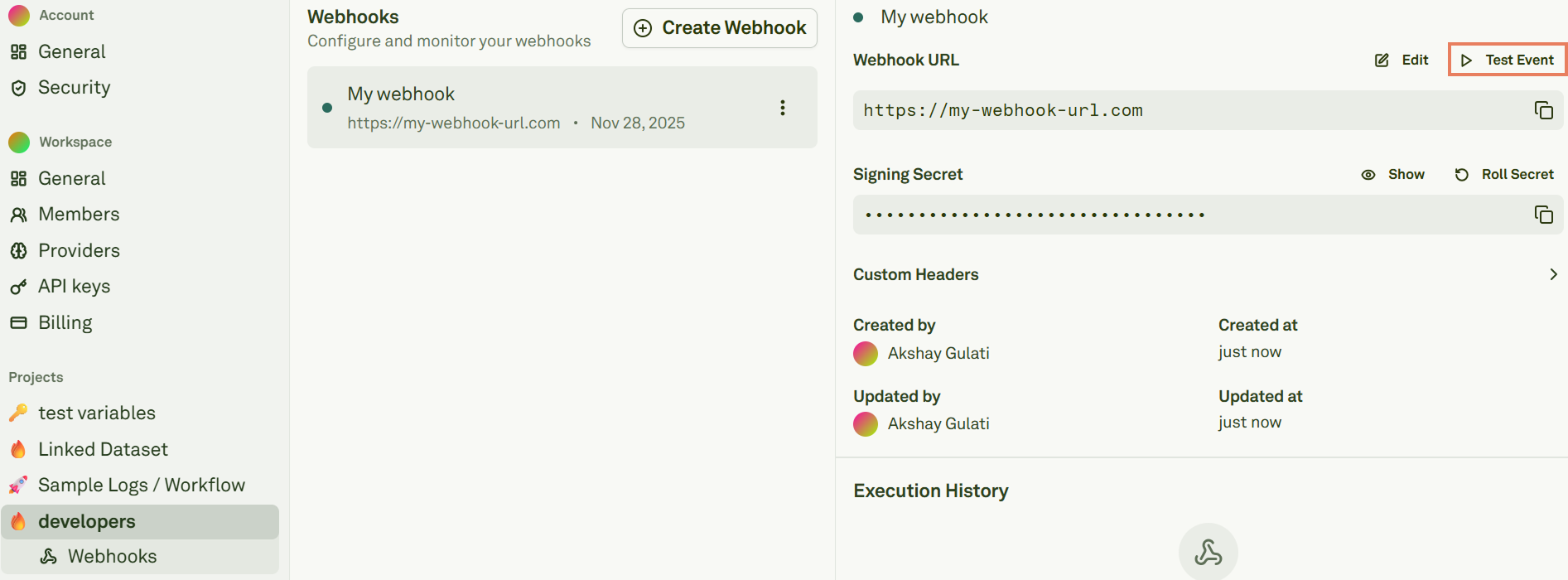
200 OK after verifying the signature.
Roll secrets
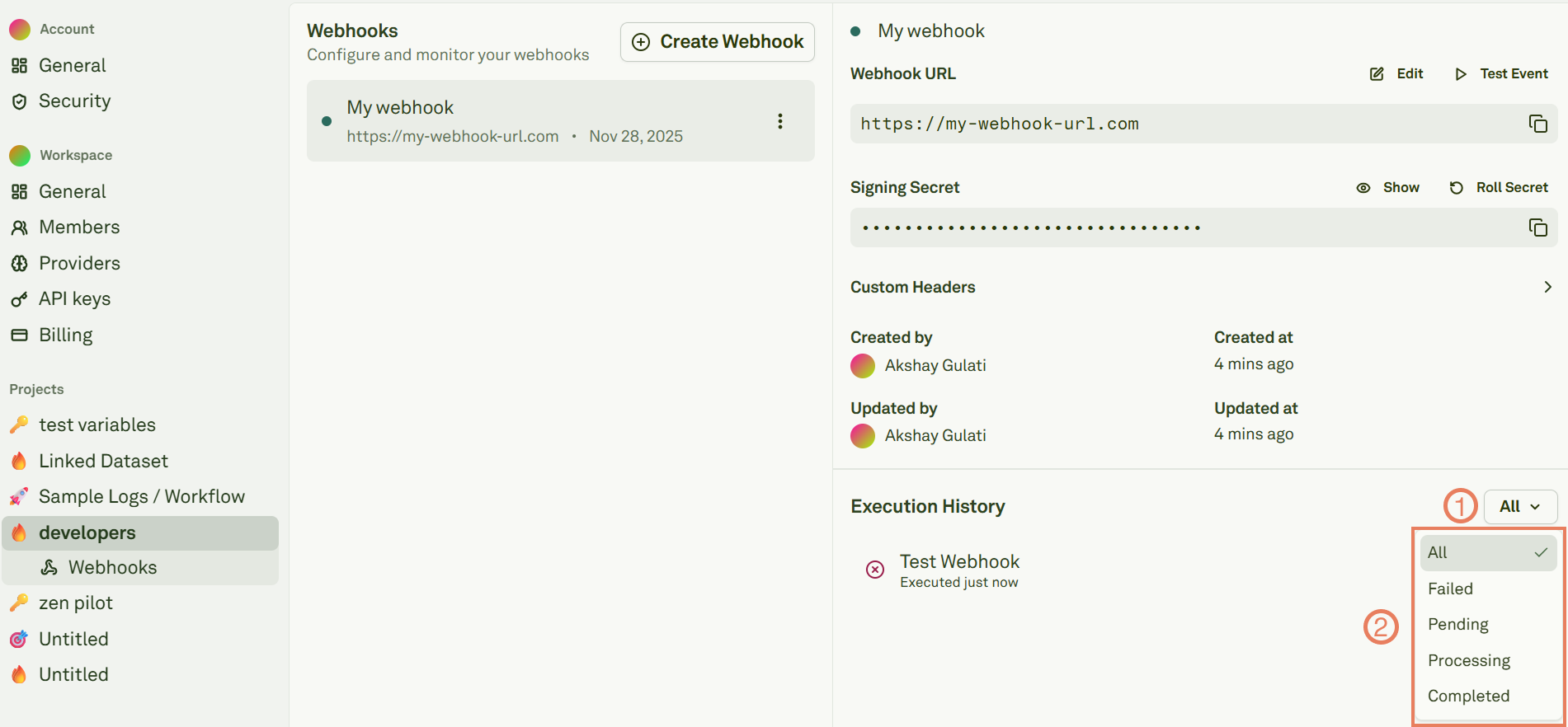
Roll the signing secret from the webhook details page: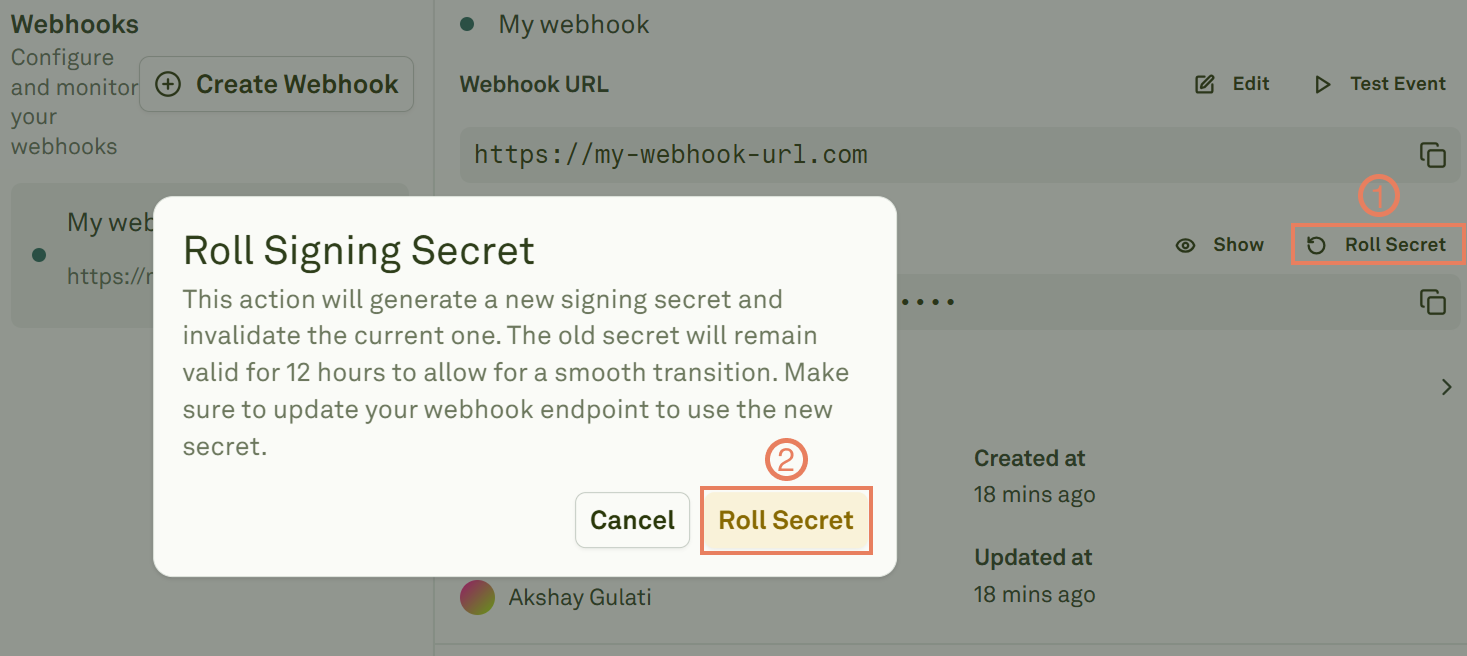
- Adaline creates a new primary secret immediately.
- The previous secret is retained as a rolled secret and remains valid for 12 hours.
- During this window,
X-Webhook-Signaturemay include multiple signatures so your server can accept either secret.
Troubleshooting
| Issue | Possible cause | Resolution |
|---|---|---|
Endpoint returns 400 or 401 | Request body was parsed/modified before signature verification. | Verify against the raw request body, not a parsed/re-serialized version. |
| Signature mismatch | Clock skew or incorrect message format. | Ensure you use the exact {timestamp}.{payload} concatenation format. |
| No signature header | Signing secret not configured or event has no body. | Confirm a signing secret is set in the webhook configuration. |
| Webhook not firing | Wrong event subscription or endpoint unreachable. | Check that the endpoint is accessible via HTTPS and the webhook is active. |
Next steps
Deploy Your Prompt
Ship prompts and see webhooks in action.
Configure Environments
Set up environments for your deployment pipeline.